PUBLISHER: Mordor Intelligence | PRODUCT CODE: 1850346

PUBLISHER: Mordor Intelligence | PRODUCT CODE: 1850346
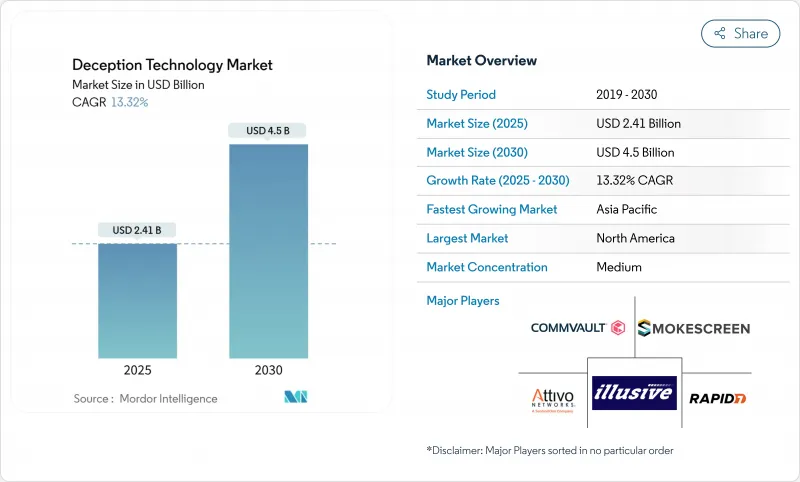
Deception Technology - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2025 - 2030)
The deception technology market posted USD 2.41 billion in 2025 and is set to advance at a 13.3% CAGR to USD 4.50 billion by 2030.
Rising zero-day exploits, AI-driven deepfake fraud, and cloud-native workload expansion compel security teams to adopt early-warning controls that spot attackers inside the network before damage occurs. Vendors now weave decoys into zero-trust micro-segmentation, giving defenders tripwires that work even when identities or endpoints are compromised. Demand also accelerates because cyber-insurance carriers require proactive lateral-movement detection as a condition for favorable premiums. Although North America keeps spending leadership, the deception technology market gains rapid momentum in Asia-Pacific as multicloud adoption surges and local regulators tighten breach-notification rules.
Global Deception Technology Market Trends and Insights
Surge in Zero-Day Exploits and Targeted APTs
State-sponsored collectives automate reconnaissance with AI, finding novel vulnerabilities faster than signature-based defenses adapt. The Institute for Security and Technology notes that automated reconnaissance compresses attacker dwell time, forcing defenders to rethink reactive playbooks. Deception platforms insert believable but fake assets that weaponize curiosity; once probed, alerts trigger in seconds while production systems stay untouched. Because detection is based on attacker behavior rather than threat-intelligence feeds, the deception technology market provides resilience against bespoke malware that evades hash-matching controls. Vendors now pre-package decoys for industrial control systems and SaaS APIs, reflecting attacker pivot toward operational technology.
Escalating Cloud-Native Workloads Broaden Attack Surface
Containerized and serverless applications can spin up and down within minutes, leaving security operations centers blind to east-west traffic. Zscaler deploys generative-AI decoys that mimic large-language-model endpoints, luring attackers into instrumented sandboxes. Because decoys scale automatically inside Kubernetes namespaces, defenders gain continuous coverage even as underlying microservices change. The deception technology market capitalizes on cloud providers' metadata APIs to place traps inside virtual private clouds without installing agents. As organizations adopt multi-cloud strategies, cross-provider decoy orchestration becomes a buying criterion, especially in regulated industries that cannot centralize logs in a single region.
Entrenched Reliance on Legacy Honeypots
Many firms still run static honeypots deployed years ago. Attackers now fingerprint such assets through protocol quirks or uptime patterns, bypassing them with ease. This sunk-cost bias delays upgrades to adaptive decoys able to morph operating-system banners or rotate credentials automatically. Legacy honeypots also demand manual log parsing, consuming resources that should focus on real attack paths. Because these tools produce few actionable alerts, boards question ROI, thereby constraining new investment and dampening growth of the deception technology market.
Other drivers and restraints analyzed in the detailed report include:
- CISO Preference for Low-Friction, Agent-Less Detection Tools
- Rise of AI-Generated Deepfake Identity Attacks
- Scarcity of Deception-Skilled SecOps Staff
For complete list of drivers and restraints, kindly check the Table Of Contents.
Segment Analysis
On-premises deployment commanded 67.9% of deception technology market share in 2024, illustrating enterprises' need to keep high-interaction decoys close to crown-jewel systems for compliance and forensic control. That control, however, brings hardware refresh cycles and change-management overhead that limit agility. Cloud deployment contributes a modest slice today but is slated to rise at a 15.2% CAGR through 2030, the fastest pace within the deception technology market. Cloud-based consoles spin up decoys across regions within minutes, making them attractive for global branch rollouts.
Hybrid models emerge as a pragmatic bridge, letting teams place sensitive database decoys on-premises while offloading analysis and scaling tasks to public clouds. As multicloud adoption rises, buyers demand single-pane views across AWS, Azure, and Google Cloud, pushing providers to invest in identity federation and immutable infrastructure blueprints. These capabilities enhance the deception technology market size for cloud modules and convince regulation-bound sectors that shared-responsibility models can still satisfy audit controls.
Large enterprises retained 70.2% revenue share in 2024 and continue shaping feature roadmaps by insisting on API depth, MITRE ATT&CK alignment, and advanced analytics. Yet SMEs now register a 14.9% growth trajectory, outpacing big-company spending within the deception technology market. Subscription-based managed deception services, billed per asset, cut entry barriers and deliver curated alerts that fit smaller teams' bandwidth.
Savings compound because cloud consoles eliminate hardware purchase, allowing SMEs to reallocate capital toward employee awareness programs. For vendors, the segment's scale effect is compelling; thousands of mid-sized customers can equal the license revenue of a handful of Fortune 500 accounts. Consequently, roadmap priorities now include low-code playbooks and automated decoy placement, features designed to compress onboarding from weeks to hours and thereby expand deception technology market size among smaller firms.
The Deception Technology Market Report is Segmented by Deployment (On-Premises and Cloud), Organization Size (Large Enterprises and Small and Medium Enterprises (SMEs)), Service (Managed Services and Professional Services), Deception Stack (Data Security, Application Security, and More), End-User (Government, Defense, BFSI, IT and Telecommunication, and More), and Geography.
Geography Analysis
North America generated 41.8% of revenue in 2024, buoyed by stringent mandates such as CISA's directive on incident reporting and a concentration of Fortune 100 headquarters that can fund specialized controls. Federal contracts increasingly specify deception capabilities, further cementing the region's leadership within the deception technology market.
Europe advances steadily as the NIS2 Directive broadens the scope of entities required to maintain proactive threat-detection programs Local vendors stress data-sovereignty features, ensuring logs stay inside EU borders. Emerging EU cloud providers now embed deception natively, offering compliance-ready bundles that appeal to mid-market industrial manufacturers.
Asia-Pacific remains the fastest-growing territory at 13.8% CAGR. Governments in Japan, India, and Singapore launch grant programs that co-fund zero-trust pilots incorporating deception. Telecom rollouts of 5G standalone cores enlarge attack surfaces, pushing operators to install signaling-protocol decoys that detect rogue base-station registration attempts. These initiatives collectively enlarge deception technology market size in the region. Meanwhile, Latin America and Middle East and Africa start integrating deception into critical-infrastructure revamps, although budget constraints and talent gaps temper near-term uptake.
- Illusive Networks
- Attivo Networks (SentinelOne)
- Rapid7
- Acalvio Technologies
- CounterCraft
- CyberTrap
- TrapX Security
- Smokescreen Technologies
- Ridgeback Network Defense
- LogRhythm
- WatchGuard Technologies
- Broadcom (Symantec)
- Morphisec
- Fortinet (FortiDeceptor)
- Zscaler
- Microsoft (Security Honeytokens)
- Akamai
- Palo Alto Networks
- Fidelis Cybersecurity
- Commvault (TrapX integration)
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions and Market Definition
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET LANDSCAPE
- 4.1 Market Overview
- 4.2 Market Drivers
- 4.2.1 Surge in zero-day exploits and targeted APTs
- 4.2.2 Escalating cloud-native workloads broaden attack surface
- 4.2.3 CISO preference for low-friction, agent-less detection tools
- 4.2.4 Rise of AI-generated deepfake identity attacks
- 4.2.5 Convergence of deception with zero-trust micro-segmentation
- 4.2.6 Cyber-insurance policies demanding proactive lateral-movement detection
- 4.3 Market Restraints
- 4.3.1 Entrenched reliance on legacy honeypots
- 4.3.2 Scarcity of deception-skilled SecOps staff
- 4.3.3 Adversary use of large-language-model recon to spot decoys (under-the-radar)
- 4.3.4 Budget cannibalization by bundled EDR/XDR platforms
- 4.4 Value Chain Analysis
- 4.5 Regulatory Landscape
- 4.6 Technological Outlook
- 4.7 Porter's Five Forces Analysis
- 4.7.1 Threat of New Entrants
- 4.7.2 Bargaining Power of Suppliers
- 4.7.3 Bargaining Power of Buyers
- 4.7.4 Threat of Substitutes
- 4.7.5 Intensity of Competitive Rivalry
- 4.8 Investment Analysis
- 4.9 Assessment of the Impact of Macroeconomic Trends on the Market
5 MARKET SIZE AND GROWTH FORECASTS (VALUE)
- 5.1 By Deployment
- 5.1.1 On-premises
- 5.1.2 Cloud
- 5.2 By Organization Size
- 5.2.1 Large Enterprises
- 5.2.2 Small and Medium Enterprises (SMEs)
- 5.3 By Service
- 5.3.1 Managed Services
- 5.3.2 Professional Services
- 5.4 By Deception Stack
- 5.4.1 Data Security
- 5.4.2 Application Security
- 5.4.3 Endpoint Security
- 5.4.4 Network Security
- 5.5 By End-User
- 5.5.1 Government
- 5.5.2 Defense
- 5.5.3 BFSI
- 5.5.4 IT and Telecommunication
- 5.5.5 Healthcare
- 5.5.6 Other End-Users
- 5.6 By Geography
- 5.6.1 North America
- 5.6.1.1 United States
- 5.6.1.2 Canada
- 5.6.1.3 Mexico
- 5.6.2 Europe
- 5.6.2.1 Germany
- 5.6.2.2 United Kingdom
- 5.6.2.3 France
- 5.6.2.4 Italy
- 5.6.2.5 Spain
- 5.6.2.6 Russia
- 5.6.2.7 Rest of Europe
- 5.6.3 Asia-Pacific
- 5.6.3.1 China
- 5.6.3.2 Japan
- 5.6.3.3 India
- 5.6.3.4 South Korea
- 5.6.3.5 Australia and New Zealand
- 5.6.3.6 Rest of Asia-Pacific
- 5.6.4 South America
- 5.6.4.1 Brazil
- 5.6.4.2 Argentina
- 5.6.4.3 Rest of South America
- 5.6.5 Middle East and Africa
- 5.6.5.1 Middle East
- 5.6.5.1.1 Saudi Arabia
- 5.6.5.1.2 United Arab Emirates
- 5.6.5.1.3 Turkey
- 5.6.5.1.4 Rest of Middle East
- 5.6.5.2 Africa
- 5.6.5.2.1 South Africa
- 5.6.5.2.2 Nigeria
- 5.6.5.2.3 Rest of Africa
- 5.6.1 North America
6 COMPETITIVE LANDSCAPE
- 6.1 Market Concentration
- 6.2 Strategic Moves
- 6.3 Market Share Analysis
- 6.4 Company Profiles (includes Global level Overview, Market level overview, Core Segments, Financials as available, Strategic Information, Market Rank/Share for key companies, Products and Services, and Recent Developments)
- 6.4.1 Illusive Networks
- 6.4.2 Attivo Networks (SentinelOne)
- 6.4.3 Rapid7
- 6.4.4 Acalvio Technologies
- 6.4.5 CounterCraft
- 6.4.6 CyberTrap
- 6.4.7 TrapX Security
- 6.4.8 Smokescreen Technologies
- 6.4.9 Ridgeback Network Defense
- 6.4.10 LogRhythm
- 6.4.11 WatchGuard Technologies
- 6.4.12 Broadcom (Symantec)
- 6.4.13 Morphisec
- 6.4.14 Fortinet (FortiDeceptor)
- 6.4.15 Zscaler
- 6.4.16 Microsoft (Security Honeytokens)
- 6.4.17 Akamai
- 6.4.18 Palo Alto Networks
- 6.4.19 Fidelis Cybersecurity
- 6.4.20 Commvault (TrapX integration)
7 MARKET OPPORTUNITIES AND FUTURE OUTLOOK
- 7.1 White-space and Unmet-need Assessment




